HIPAA Compliance Statement
HIPAA Compliance & Patient Privacy
Leaa Health is committed to protecting the privacy, security, and confidentiality of patient information in accordance with the Health Insurance Portability and Accountability Act (HIPAA) and applicable federal and state laws.
All medical services are provided by licensed healthcare professionals. Any Protected Health Information (PHI) collected, created, used, or disclosed by Leaa Health is handled solely for purposes of treatment, payment, and healthcare operations, as permitted by law.
Leaa Health maintains administrative, physical, and technical safeguards designed to protect patient information against unauthorized access, use, or disclosure. Access to PHI is restricted to authorized personnel and service providers who are required to comply with HIPAA privacy and security standards.
Leaa Health does not use patient medical information for advertising or marketing purposes without proper written authorization. Any third-party vendors that may have access to PHI are required to enter into Business Associate Agreements (BAAs) to ensure continued HIPAA compliance.
For questions regarding privacy practices or HIPAA compliance, please contact:
privacy@leaa.io
Join leaa’s over 40,000
happy & healthy customers
call to join
Name: Samantha R.
Location: SoHo, NYC
Rating: 5★
Review:
“Leaa Health is a total game changer. I booked a same-day home visit for my father who had flu symptoms while visiting from London. The doctor arrived within 90 minutes, was incredibly professional, and even brought a rapid test kit. We avoided a chaotic ER visit, and my dad was feeling better within hours. Concierge healthcare at its best!”
Name: James L.
Location: Miami Beach
Rating: 5★
Review:
“From booking to follow-up, Leaa’s service was seamless. I use the Elite Plan for my family and it’s worth every dollar. We’ve had multiple visits in-home for IV therapy, testing, and even travel clearance. Their providers are top-notch, and the peace of mind is priceless when you have kids. Highly recommend for busy professionals or anyone who values comfort and safety.”
More reviews
“ Thank you for choosing
leaa’s medical house calls "
Star Power
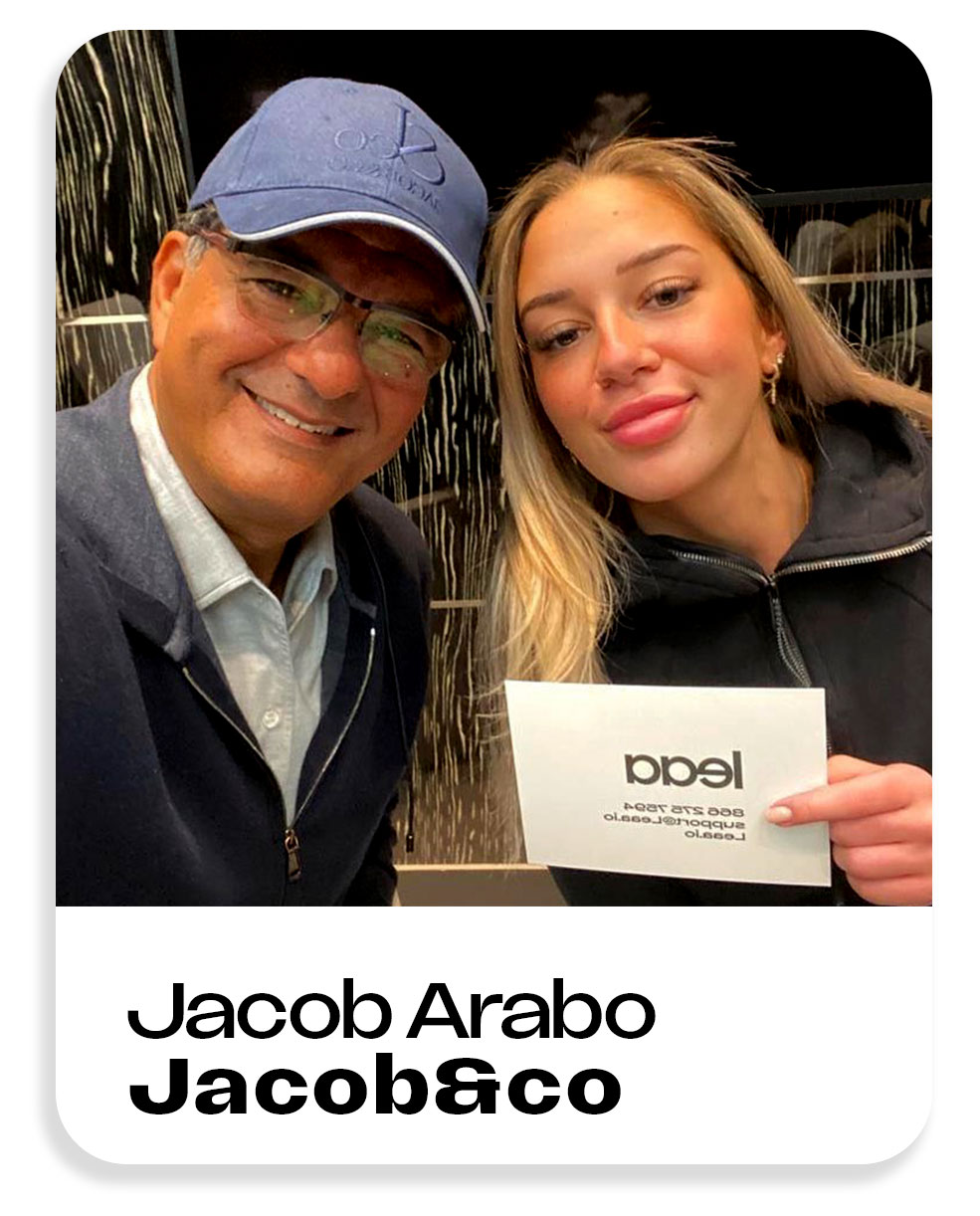
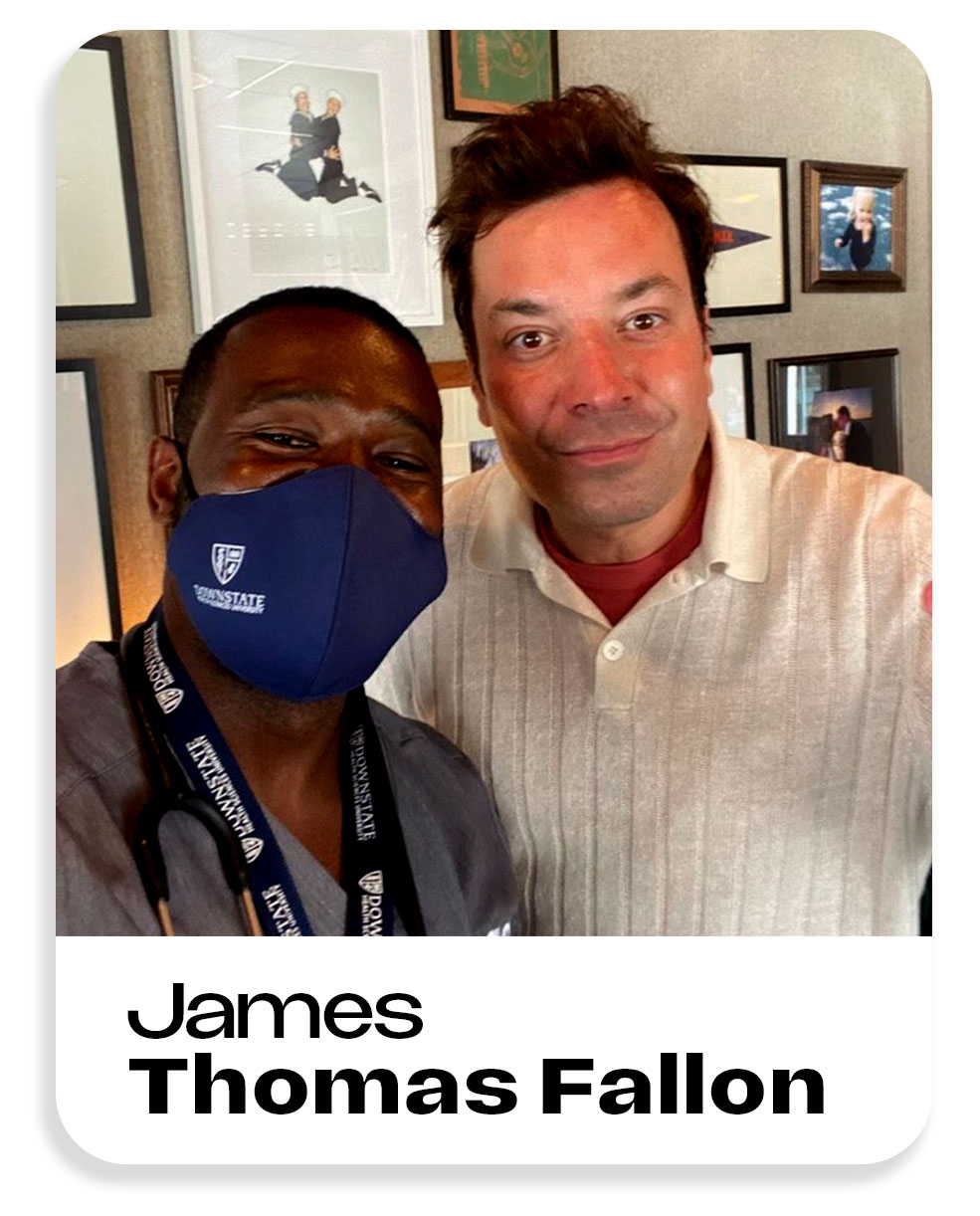
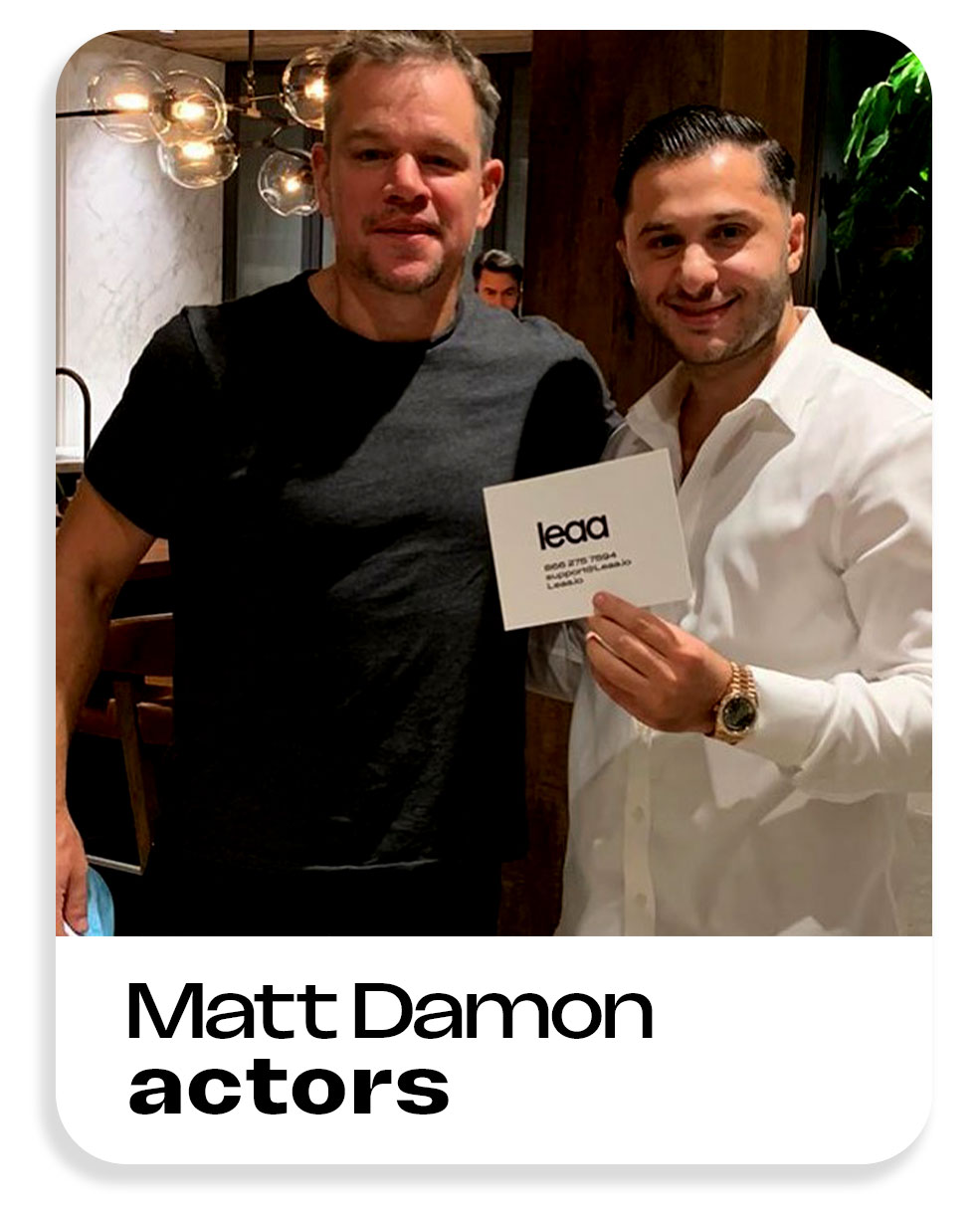
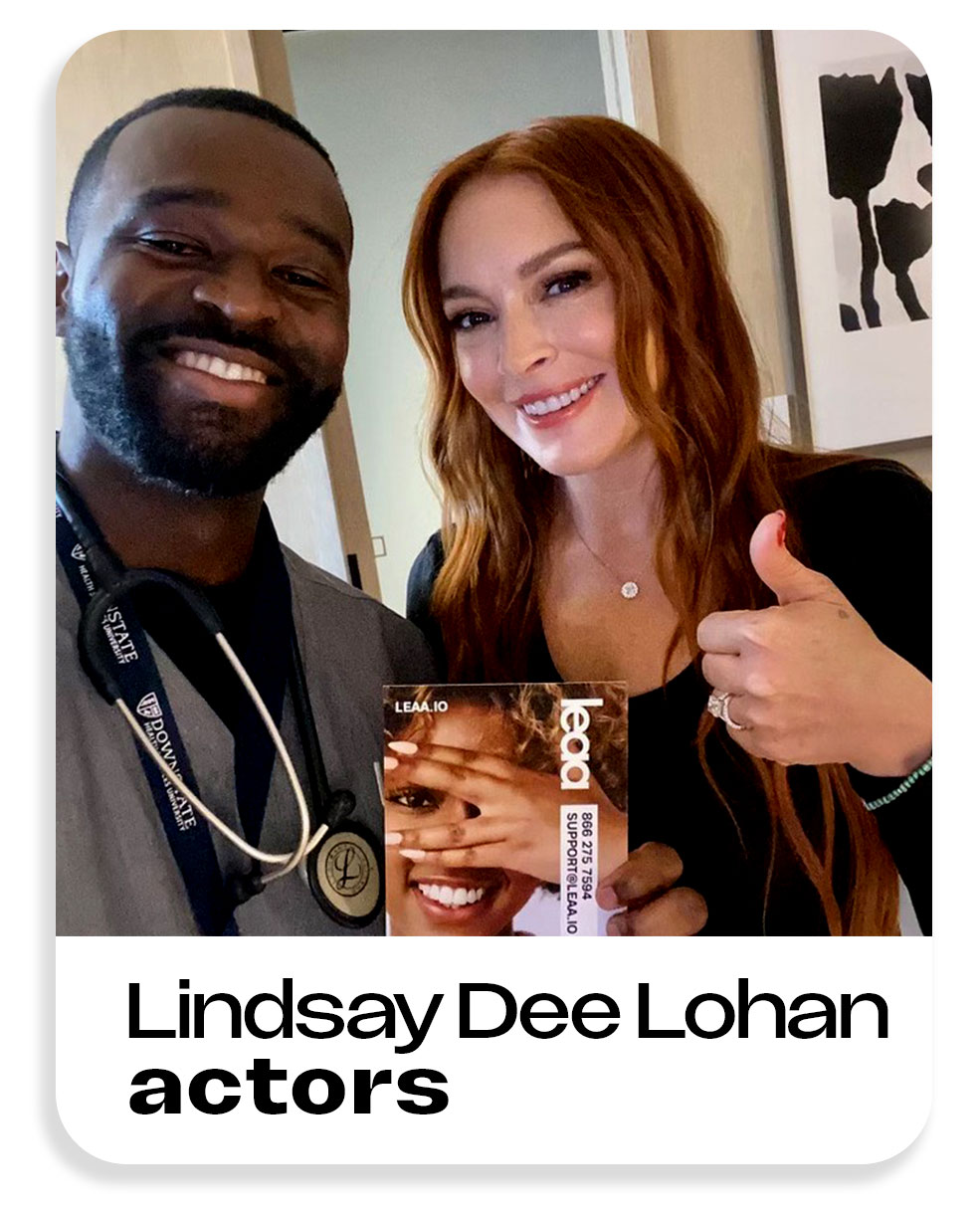
Our clients
SoftBank, Disney, ViacomCBS (now Paramount Global) ,Uber, Sharing, Nike, Atlantic Records, American Eagle Outfitters, Warner Bros, New York Rangers (NHL), Jacob & Co, ZARA, Eileen Fisher, Target and more.
Service Areas
Leaa Health provides home doctor visits in:
New York City
Upper East Side, Tribeca, SoHo, Battery Park City, Chelsea, Lincoln Square, and more
Brooklyn
DUMBO, Cobble Hill, Brooklyn Heights, Williamsburg
New Jersey
Short Hills, Montclair, Hoboken, Saddle River, Tenafly, Jersey City
Miami, FL
Aventura, Coral Gables, Brickell, Coconut Grove, Miami Beach
Texas
Dallas-Fort Worth Area, Houston, Austin, San Antonio, Prosper, Celina
We also serve surrounding areas and special requests — Leaa goes where care is needed.
More states launching soon!
(Treatment prices do not include the home visit convenience fee,
Note: leaa members get 20% off all treatments. No insurance
VISITING PHYSICIANS NETWORK PC- Home Doctor Visits LEAA EST 2017
Copyright © Allure Before and After Corp. All rights reserved.
All content on this website—including AI technology, images, and the support/booking system—is protected by copyright and remains the exclusive property of Allure Before and After Corp.
Leaa Health operates under a valid licensing agreement, which grants limited rights to use these proprietary materials. Unauthorized use, duplication, or redistribution of any part of this content is strictly prohibited. Prices, services, and availability are subject to change without notice.